30 WordPress Plugins Got Backdoored Because Nobody Audits Plugin Sales

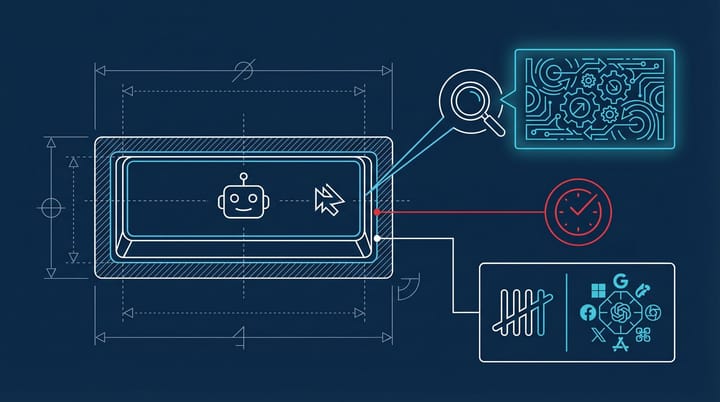
If you run a marketing site on WordPress (and roughly 43% of all websites do), every plugin you have installed carries implicit trust. Trust that the developer is who they say they are, trust that updates contain what the changelog says they contain, and trust that if the plugin gets sold to someone new, someone somewhere is vetting the buyer.
That last part? Nobody is doing that. And it just cost hundreds of thousands of sites.
On April 7, WordPress.org permanently closed 31 plugins from the Essential Plugin author group, all on the same day. The plugins included widely installed tools like Blog Designer, Popup Anything, Accordion, and Countdown Timer Ultimate. They had been acquired through a six-figure deal on Flippa by a buyer identified only as "Kris." Within months of the acquisition, every single one contained a backdoor.
The attack was patient, not sophisticated
The actual injection was, in the words of the security researchers who dissected it, a "textbook arbitrary function call." Version 2.6.7, released August 8, 2025, added 191 lines of PHP code including a deserialization vulnerability tucked inside a file called class-anylc-admin.php. The plugin's wpos-analytics module phoned home to a remote server, pulled down a backdoor file, and used it to inject roughly 6KB of malicious PHP into wp-config.php.
The clever part was not the code. It was the timing.
The backdoor sat dormant for eight months. Eight months of normal updates, normal changelogs, normal behavior. Then on April 5, 2026, it activated. SEO spam injection, command-and-control routing through Ethereum smart contracts, all of it. The whole weaponization window lasted about 6 hours and 44 minutes on April 6, between 04:22 and 11:06 UTC.
A client of Anchor Hosting got a WordPress dashboard security notice. Their hosting provider's forensic analysis, using daily restic backups, pinpointed exactly when the injection happened. WordPress.org shut everything down the next day and pushed a forced auto-update to a clean version.
WordPress.org has no ownership transfer review
This is the part that should bother you more than the backdoor itself. WordPress.org has no mechanism to flag or review plugin ownership transfers. When a plugin changes hands, the new owner inherits full commit access to the WordPress.org repository. No additional code review gets triggered. No "change of control" notification goes out to the hundreds of thousands of people who installed the plugin. Nothing.
The official guidance from WordPress.org essentially says: if you sell your plugin, make sure the new owners understand the guidelines. They recommend "only giving your plugin to people you personally have vetted." For a platform that powers 43% of the internet, that feels pretty casual.
And this is not isolated. The same week, a separate attack hit Smart Slider 3 Pro through compromised update infrastructure, pushing a malicious version that was live for about six hours before anyone caught it. According to FatLab Web Support's research, plugins account for 91% of all WordPress ecosystem vulnerabilities, and 20% of those vulnerabilities get exploited within six hours of disclosure.
I keep coming back to what this looks like from the attacker's perspective. You find a portfolio of 30 plugins with hundreds of thousands of installations, buy them through a legitimate marketplace, wait eight months to build trust, then flip the switch. The total investment is six figures. The potential return, in terms of SEO spam injection across that many sites, is substantially more. It is an arbitrage play, and the marketplace that makes it possible has essentially zero gatekeeping.
This has been the pattern for years now. A plugin called Display Widgets was sold for $15,000 a few years back and immediately weaponized with payday loan spam injection. The ecosystem treated it like an isolated incident. But when the same playbook works every time, calling it isolated stops making sense.
This matters more to marketing teams than they realize
If you are running a WordPress marketing site (and honestly, most mid-market marketing teams still are), your plugin list is a supply chain you have probably never audited. I am not talking about the big, well-known plugins like Yoast or WooCommerce. I am talking about the gallery plugin someone installed three years ago, the accordion widget sitting in your footer since the last redesign, or the popup tool your previous agency left behind.
Those are exactly the kinds of plugins that get acquired in deals like this. Small enough to fly under the radar, established enough to have a real install base, and maintained just enough that WordPress.org does not flag them as abandoned.
A rough benchmark, from what I have seen across marketing WordPress installations: if you have more than 15 active plugins and have not reviewed the author or ownership of each one in the last year, you almost certainly have at least one whose ownership has changed without you knowing. That is not really a prediction. It is just the math, given how frequently these transfers happen on marketplaces like Flippa.
The Google implications are worth thinking about too. If an attacker injects SEO spam into your wp-config.php, your site can start serving cloaked content to crawlers without your pages looking any different in a browser. By the time you notice your rankings dropping or a manual action landing in Search Console, the damage is already indexed. We covered a similar enforcement dynamic with Google's recent spam policy changes around back button hijacking, and the pattern is consistent: Google does not distinguish between "you got hacked" and "you did this on purpose" when it applies spam signals.
Audit your plugin stack before Google's crawler does
First, check if any of the 31 affected plugins are on your site. The full list is published in Anchor Hosting's investigation and includes common tools like Blog Designer, Popup Anything, Countdown Timer Ultimate, WP Logo Showcase, and Hero Banner. If you find one, apply the patched version immediately and inspect your wp-config.php for unusual code blocks. The injected payload was roughly 6KB, so a file size comparison against a clean install is a decent first check.
Second, even if you are not directly affected, pull up your full plugin list and check who actually maintains each one. Look at the "Author" field in your WordPress dashboard, then check the plugin's page on WordPress.org. If the author has changed in the last 12 months, or if the plugin has not been updated in over a year, that is your shortlist for removal or replacement.
Third, set up file integrity monitoring if you have not already. Tools like Wordfence or Patchstack will flag changes to core files like wp-config.php. This is the kind of thing that would have caught the injection within hours instead of letting it run for a full exploit window.
And if you manage WordPress sites for clients, this is probably worth a 5-minute conversation at the next check-in. "Hey, we audited the plugin stack, here is what we found" is the kind of proactive communication that keeps accounts. Discovering a backdoor after a client's rankings crater is the kind that loses them.
The uncomfortable reality is that the WordPress plugin ecosystem works on a trust model designed for a much smaller, more community-driven platform. At 43% of the web, that trust is probably overextended. Auditing your plugin stack is not glamorous work, but it is a lot cheaper than explaining to a client why their site is serving casino spam to Googlebot.
Notice Me Senpai Editorial