Every Google-Certified CMP Failed the Opt-Out Audit (All 11 of Them)
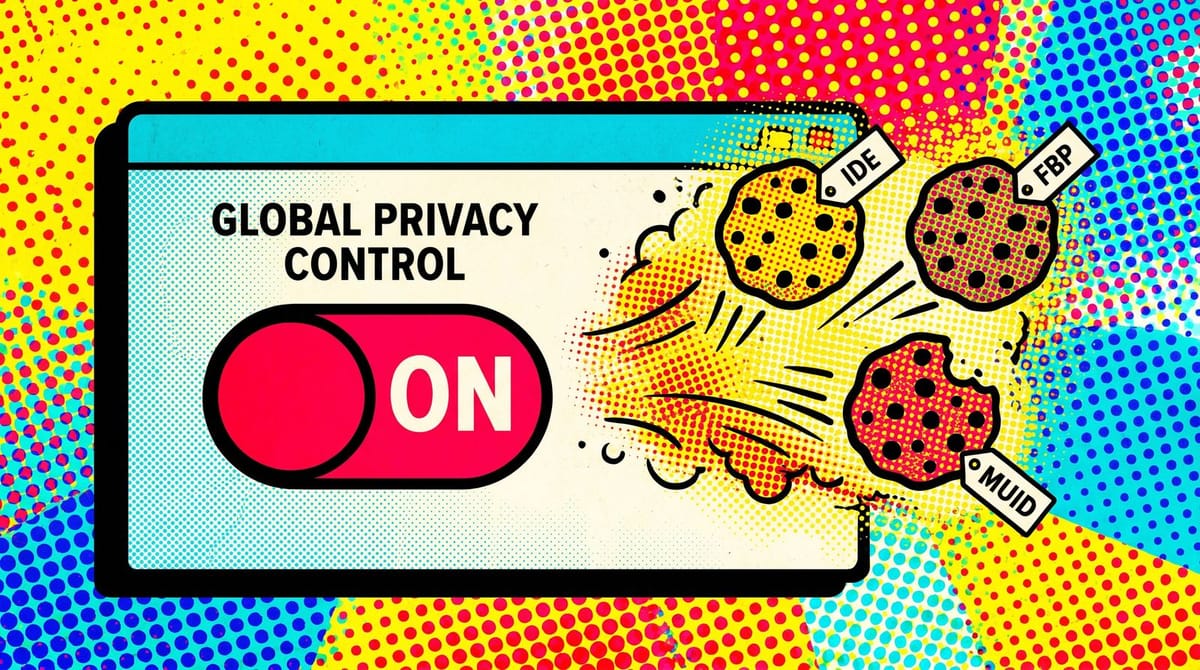
webXray scanned 7,634 California websites in March 2026 and ran every page twice: once with the Global Privacy Control opt-out signal enabled, once without. Eleven Google-certified consent management platforms were in the sample. All 11 failed. Advertising cookies fired on every site regardless of the GPC flag, exposing roughly 4,170 non-compliant sites to an estimated $5.8 billion in potential CCPA liability.
The headline everyone read and the finding buried beneath it
The version going around in group chats reads: Google ignores opt-outs 86% of the time, Meta 69%, Microsoft 50%. That is bad. But the part that actually matters for a working marketer is in the appendix of the webXray report: every single Google-certified CMP they tested fired advertising cookies after the user opted out. The three named anonymized providers missed at 77%, 90%, and 91% respectively. The aggregate across all 11 Google-certified vendors was 100% failure.
You paid for a consent management platform to prevent exactly this. It did not.
Quick context if you have not had to care about this lately. Global Privacy Control is a browser-level signal, sent as a single HTTP request header, Sec-GPC: 1. The California Attorney General formally accepts it as a valid CCPA opt-out. Colorado and Connecticut accept it for their state laws too. Users can enable it through extensions, Brave, DuckDuckGo, and Firefox natively. For a vendor to respect it, the server has to do something specific: read the header, then refrain from returning a set-cookie. The vendors in this audit all did the first part. None did the second.
Dr. Timothy Libert, who led cookie policy at Google until 2023 and now runs webXray, summarized the problem to 404 Media: "In my view this stuff isn't complicated. You say, 'don't set the cookie.' They set the cookie." The Sec-GPC: 1 header is a single-byte signal. Google, Microsoft, and Meta all receive it. None of them treat it as a stop instruction.
What actually fired, cookie by cookie
On Google's side, the audit caught the IDE cookie firing after opt-out on 77% of sampled sites. Also __gads, __gpi, FPAU, FPGSID, __Secure-YNID, and VISITOR_INFO1_LIVE. 11,021 advertising cookies set across the sample despite GPC, a number that matters because most CMP implementations rely on a client-side check that Google's ad servers do not need to obey.
Microsoft returns the MUID cookie from .bing.com with a one-year TTL, unconditionally. 7,550 instances in the sample. Microsoft's line, via its statement to reporters, is that certain cookies are "necessary for operational purposes." That argument has been thin for a while. Operational cookies do not belong on an advertising domain.
Meta's Facebook Pixel, which sits on an estimated 5.8 million websites, has no code path that checks the GPC header. The _fbp cookie fires when the pixel loads. No conditional. The company's response was to call the audit "a marketing ploy," which is rhetoric, not a rebuttal.
Why the CMP you're paying for can't fix this
The architecture of every CMP I've looked at is the same. The CMP sits in front of the tag manager, reads the user's preference, and either unblocks or blocks the tag from firing. It does this client-side. Once the tag fires, the CMP has no authority over what the vendor's server does with the request.
Google's ad server, on receipt of Sec-GPC: 1, is supposed to respond with HTTP 451 and no cookies. Per webXray, it responds with set-cookie anyway. The CMP cannot stop this. It is not in the path. It is, at most, telling the pixel not to fire. If the pixel fires anyway (because the publisher loaded it conditionally but not correctly, or the CMP timed out, or a subsequent script re-loaded it), the server will set an advertising cookie regardless of the signal in the HTTP header.
This is why the 100% CMP failure number is not really a story about CMP vendors. It is a story about an enforcement model that assumes client-side controls can bind server-side behavior. They cannot. And regulators, so far, have mostly declined to test the assumption in court.
The enforcement math is starting to close
The CCPA penalty schedule runs $2,500 to $7,500 per violation. Prior settlements suggest regulators have figured out how to price these at scale: Sephora paid $1.2 million in 2022, Healthline Media paid $1.55 million in 2025, Walt Disney paid $2.75 million in February 2026, and PlayOn Sports paid $1.1 million in March 2026. Average settlement: roughly $1.4 million. Multiply that across the 4,170 non-compliant sites webXray flagged and you arrive at the $5.8 billion aggregate number The Record reported.
That math is a ceiling, not a forecast. Most of those sites will never get looked at. But the California AG's office has been cherry-picking sites with high traffic, a known vendor stack, and a visible GPC failure. If your site gets meaningful California traffic and runs Google Ads plus Meta Pixel through a certified CMP, the audit just handed regulators a ready-made defendant list.
The audit you can actually run on Monday
The fix is less complicated than the compliance industry suggests. From what I have seen, most teams never sniff their own traffic. Here is roughly the minimum:
- Install the Global Privacy Control extension in a fresh Chrome profile. Load your site. Open DevTools, go to Network, filter on "cookie" in the Response Headers column, and sort by domain. You are looking for set-cookie headers from google.com, doubleclick.net, facebook.com, and bing.com.
- If any advertising cookie (IDE, _gads, _fbp, MUID) shows up on a response where the request carried Sec-GPC: 1, your opt-out is theater.
- Compare against what your CMP's reporting dashboard says happened. Most CMPs will show green. Your network traffic will show red. That gap is the story.
- Do the same pass with your California traffic segment filtered in GA4, assuming GA4 is still telling the truth, which based on what we covered earlier this year is a generous assumption. Any discrepancy between CMP-reported opt-ins and set-cookie events is defensible evidence you flagged the issue.
You are not going to solve the server-side problem from inside a CMP. What you are doing is documenting, for your own legal team, that you noticed. In an enforcement action, that is the difference between "willful" and "negligent," which is the difference between the $7,500 and the $2,500 per-violation penalty.
The unflattering part for everyone
Honestly, I do not think the big platforms get fined meaningfully over this. Google will argue its products are being misunderstood (it already is). Meta will argue the pixel is a publisher tool (it is, technically). Microsoft will argue MUID is operational (it is not, but the burden sits with the regulator).
The people who will pay are the publishers and advertisers running the stack. And their defense, more or less, is going to be: the CMP said it was fine. Which webXray just proved is not a defense anyone can lean on.
It is worth sitting with that for a second. The compliance industry sold a product. An independent researcher tested the product. The product did not work. And the upcoming June 15 consent rewrite is going to move more of the attribution layer onto the same client-side signals that just failed an audit.
The networks shift toward server-side enforcement slowly. Regulators move faster than that now. From what I have seen, the teams who sniff their own traffic this month will have an answer when somebody asks. The rest will find out what their CMP actually does the day a letter arrives.
By Notice Me Senpai Editorial